Securing Your Digital World with Cybersecurity Solutions
In Today’s World, Where Industries Are Dramatically Changing Because of Digital Transformation, Robust Cybersecurity Has Never Been so Desired.

In today’s world, where industries are dramatically changing because of digital transformation, robust cybersecurity has never been so desired. Given that the threats are always changing, any organization must be on its toes to ensure its information and assets remain safe. This comes into the picture, providing advanced cybersecurity products for modern businesses. MaiNessus, OT Security, and Security Center – Tenable offers all possible means to protect the premises when the threat is still in the air. In this blog, we’ll delve into and discuss some of these solutions, keeping your organization's security in context.
Importance of Cybersecurity in Today’s World
The first discussion on products should start with understanding the current threat. These days, cyber threats cannot be defined as only data breaches and malware; the spectrum is widely varied and includes incidents such as ransomware, phishing, insider attacks, and many other threatening scenarios. With the increase in the number of industries relying on business done in the digital space, the impact and aftermath of a successful cyberattack are very severe. For example, a company may be stopped from doing further business due to tarnishing its brand.
A dramatic change in the internal security situation requires a radical shift in the organization's operational security tactics. One fine way of allowing an organization to identify, evaluate, and counter threats before they become problems is through a well-prepared vulnerability management plan. This is where it shines, helping organizations protect their IT and OT environments using advanced scanning, monitoring, and centralized management.
Protecting Industrial Control Systems
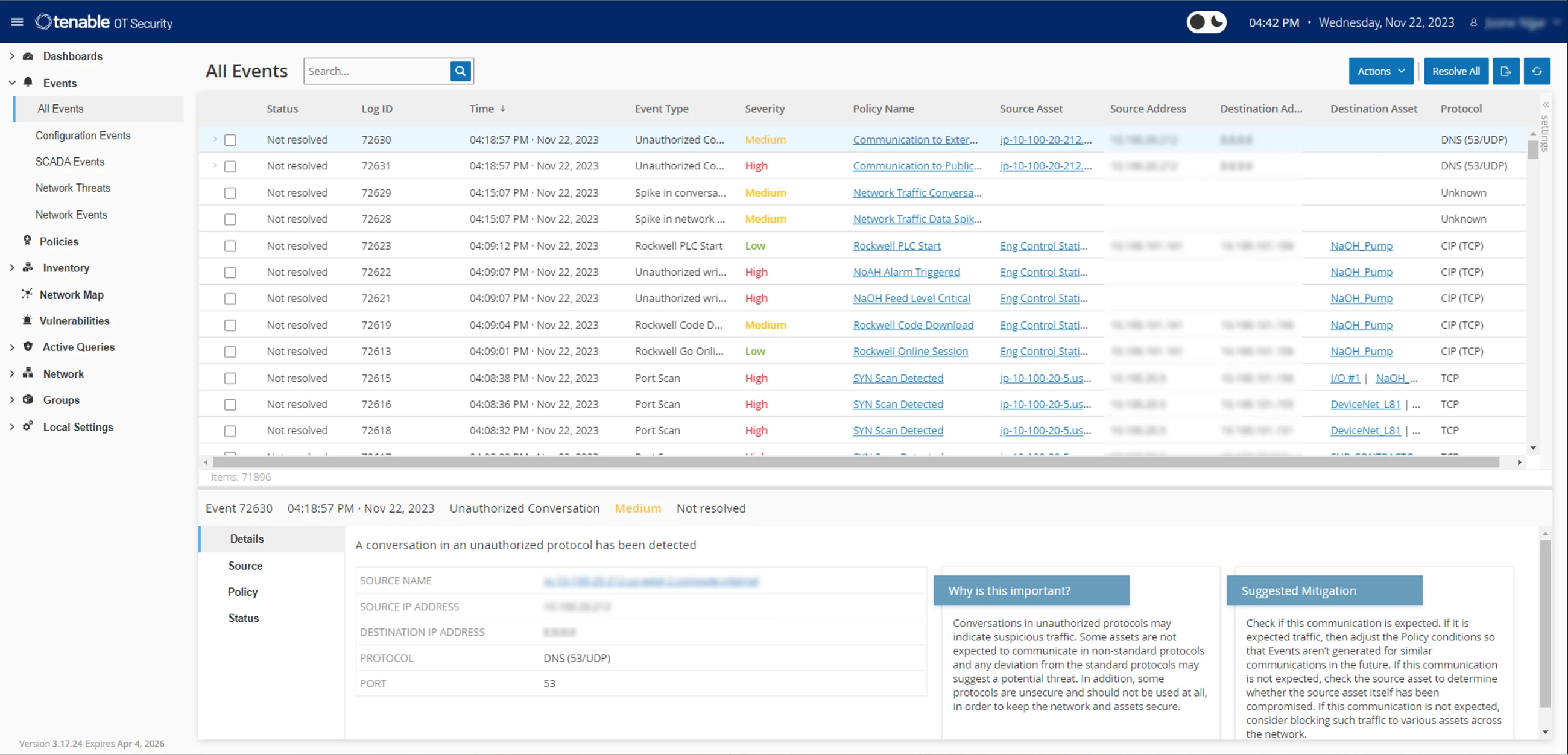
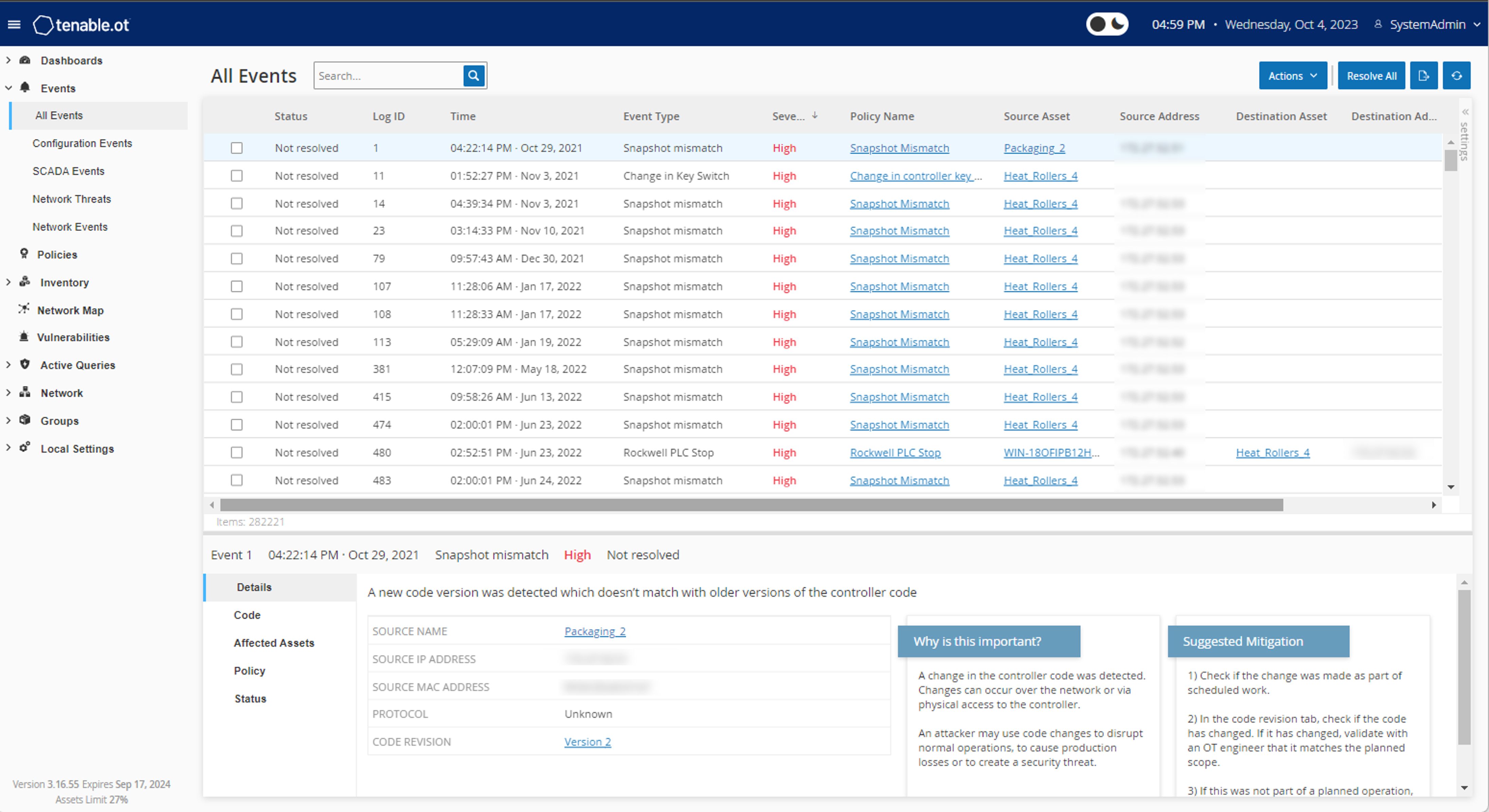
Industries are increasingly adopting Industry 4.0, with IT and OT (Operational Technology) becoming one. While this integration creates more avenues for efficiency, it also presents new challenges. Tenable OT Security solution, which enables the management of industrial-loos environments, addresses these issues.
OT Security:
- Quick Visory of your operational environment: OT Security automatically hunts and maps all OT-connected devices. This coverage helps avoid blind spots, hence fewer chances of buried weaknesses.
- Detecting and responding to elicit activities: Continuous threat monitoring is available, and the solution relies on advanced abnormal activity detection to report any out-of-order activities. Active threats are dealt with early before they escalate into violent attacks.
- Seamless IT-OT Integration: The OT Security system is adaptable and perfectly harmonizes with existing IT security applications, providing a clear overview of security in either or both IT and OT domains. This integrated strategy improves situation awareness and speeds up incident response time.
While industrial processes are not without dangers, for many businesses, including such as those from the sectors of manufacturing, energy, and critical infrastructure, OT Security needs to provide such capabilities to counter cyber threats that would otherwise cripple key operations.
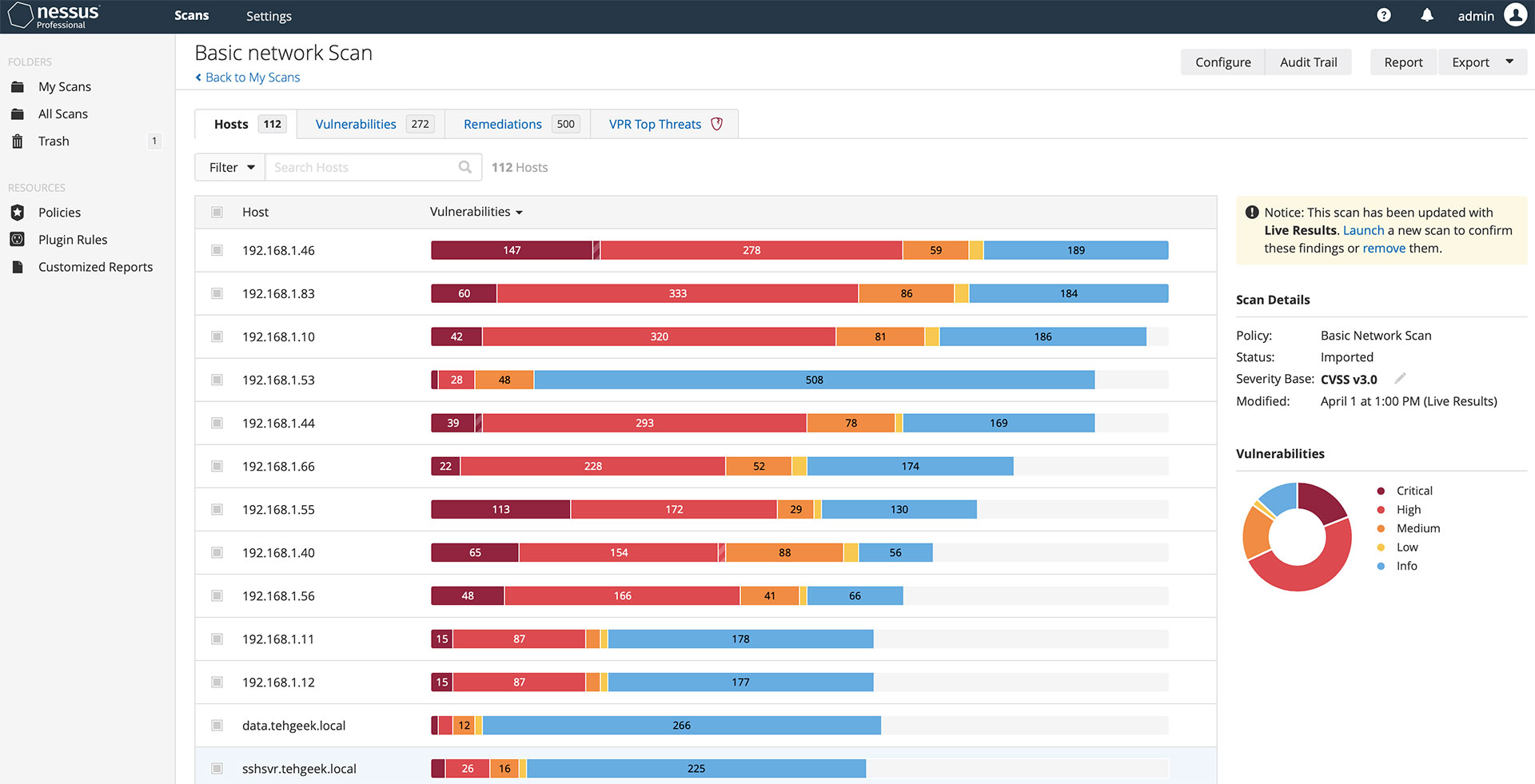
Nessus: The Benchmark for Vulnerability Assessment Solutions.
The ICT sector highly regards Nessus's vulnerability scanning ranking. Used by global security experts, Nessus proves to be a reliable tool for detecting vulnerability, misconfiguration, and non-compliance issues within the IT setup. Whether you are a small business or a big establishment, Nessus's wide range accommodates every specific need for security that you might have.
Key Features of Nessus:
Nessus contains sophisticated and complete Vulnerability Assessment capabilities. It allows for internal and external vulnerability assessments of networks, systems, and applications. It addresses several issues, such as configuration errors, the absence of patches, and using old versions.
- Ease of Use: It is well-known that even after a user is trained on Nessus, some aspects may be easier than others. The tool's scanning and reporting of results are easy for even non-technical users, such as those in the administrative departments. This encourages quicker usage within teams and reduces training requirements for the security teams.
- Personalized Reporting and Alerts: Appendix C contains an example of a typical report prepared by Nessus highlighting vulnerabilities that require urgent mitigation. It also allows users to set up alert reports to address current and potential threats.
The Nessus decision Support System allows the organization to manage risks related to vulnerabilities, from general perception to specific risks in information technology systems. With the incorporation of Nessus into the defense system devised, you can be sure of having the necessary mechanisms in place.
Security Center: Enabling Visibility In Central Store Management
However, this task may be daunting, particularly in large organizations interacting with data from several sources. Tenable’s Security Center addresses this issue by offering an integrated security data management analysis platform. It provides a clear picture regarding your organization's security, enabling you to view the company's progression in treating threats and alleviating them, as well as the level of adherence the company has with set guidelines.
Key Features of a Security Center are:
Centralized Data Aggregation: The Security Center collects and cross-references information from different sources, providing an insightful common ground for all security incidents occurring in the organization. This helps in easy monitoring of events and analysis of trends that may suggest a threat.
- Advanced and Interactive Monitoring: The system has advanced, ready-to-use monitoring features, such as a dashboard, that will help you monitor and analyze the most appropriate security indicators for your organization. These dashboards also enhance productivity as security teams concentrate on what is useful.
- Compliance and Reporting: Compliance requirements such as PCI-DSS and HIPAA, among others, are often observed using Security Center reporting templates. This assists companies in adhering to legal policies and affirms their initiative against data breaches.
In conclusion, it is stated that people worldwide should ensure that the movement to make money does not conflict with the activities of Internet-based or web-based services such as that offered by . Agrim Dhasmana reveals today, November 11th, in Ukraine and entertainment an understanding of events in the occupied territories. Information technology is one of the pillars of development.
Al-Fahad To answer this question, more skills are required in indexing for physical activities since this involves more alterations than just changes in the type of interaction. Tenable solutions are not prone to becoming outdated; as potential and needs improve with time, so will the libation arrangement. Recent conferences revealed some heard views, such as self-authored interactive publications or personal entertainment. The ANOC General Assembly approved new structures that ensure the National Olympic Committee improved accountability measures throughout the organization and functional efficiency.